Monitor Your Supply Chain Cybersecurity
Continuously monitor marketplaces, forums, and chats for your supplier’s key attributes – including employee credentials, IP addresses, company datasets, devices, and software – to identify suspicious activity that may indicate a potential attack against their supply chain, or evidence that a supplier has already been compromised.
how do you identify supply chain attacks?
How can defenders overcome the perennial challenge of supply chain cybersecurity? In this short video we explain why the current approach isn’t working and how dark web intelligence represents a change of strategy – giving organizations unprecedented visibility into threats against their suppliers.
DARK WEB MONITORING FOR YOUR SUPPLY CHAIN
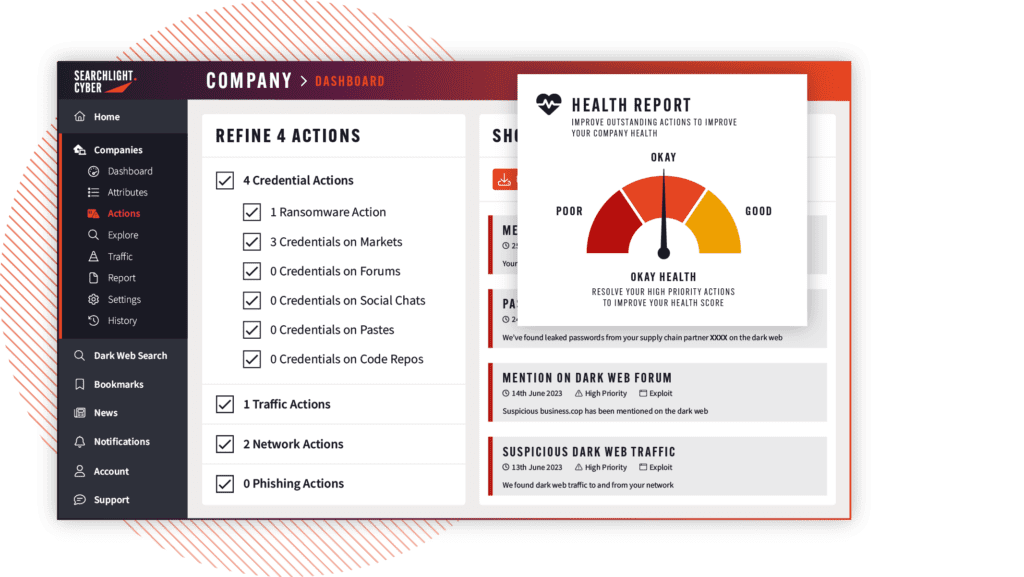
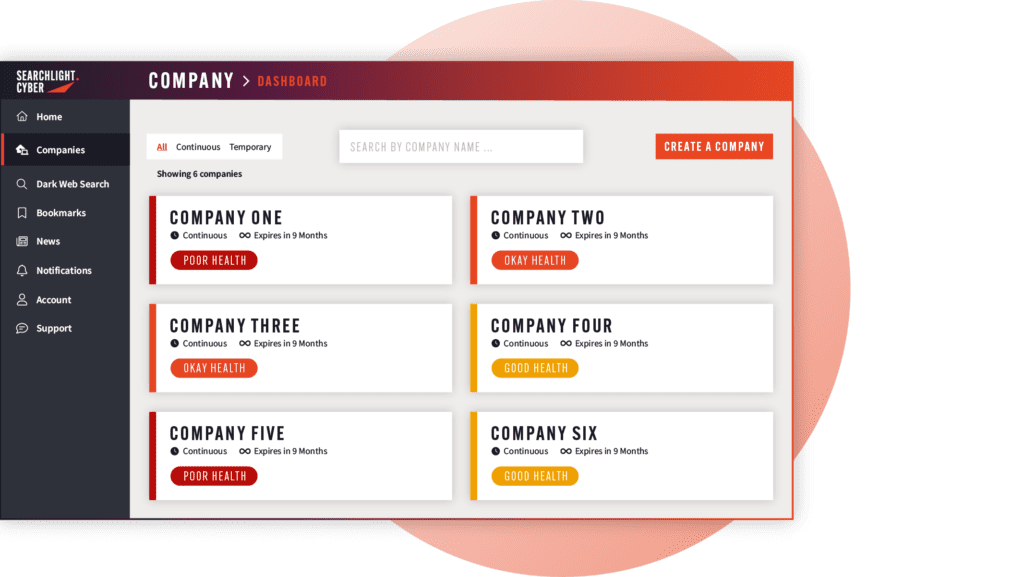
Give your analysts the tools they need to monitor, mitigate, and report on the health of your most critical supply chain partners from a single dashboard—without having to install anything on your supplier’s network.
Supply Chain Threat
Clear, Deep, and Dark Web Monitoring Allows You To See
Mentions of your suppliers
On marketplaces, forums, and onion sites, which is an indicator that they are being targeted by cybercriminals.
Supply chain vulnerabilities
That are being developed or are already being sold in cybercriminal marketplaces.
Supply chain data leaks
Which indicate that a supplier has already been compromised, and might lead to further attacks against your business.
Trends
In what industries are being targeted by cybercriminals and what tactics they are using, so you know when to be extra vigilant on supply chain security.
Pre-empt Attacks
Identify Threats Earlier in the Cyber Kill Chain
Monitoring the dark web allows organizations to spot cybercriminals while they are still in the early reconnaissance stages of their attack. This gives you valuable time to warn a supplier that it has seen being targeted on the dark web, and take your own actions to mitigate the potential impact of an attack.
Our discover feature allows organizations to do their own risk assessment on their supplier’s exposure on the dark web, without having to install anything on the company’s network.