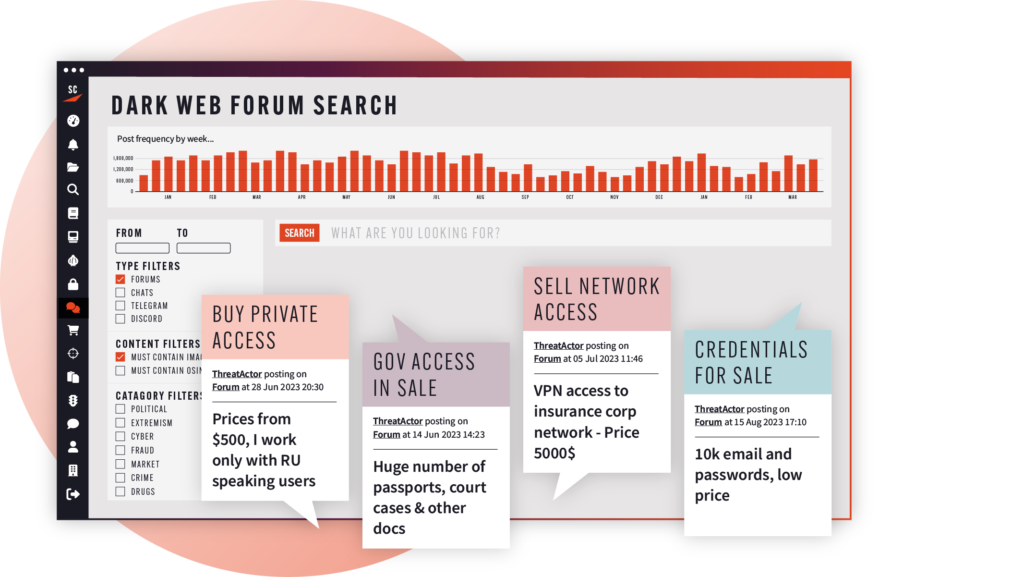
Identify Imminent Threats
SOC teams are consistently looking for context that helps them to more quickly differentiate between anomalous activity and a true cybersecurity threat. Adding dark web monitoring capabilities enriches your alerts with pre-attack intelligence, giving you the ability to spot serious incidents earlier in the Cyber Kill Chain.

Context Enrichment
Supplement alerts from other cybersecurity tools with context from the dark web, where cybercriminals conduct the reconnaissance and develop the resources for their attacks. Use dark web intelligence to interrogate anomalous behavior, and understand if suspicious activity on your infrastructure is the result of criminals’ actions on the dark web.
Track Dark Web Traffic
Use the only platform that shows live Tor traffic going to and from your network. Identify spikes to infrastructure components that may indicate cybercriminal reconnaissance or traffic from your network that could indicate insider threat.

Dark web data
Monitor Cyber Threats
Deep and dark web marketplaces and forums
Intercept chatter about your organization, new vulnerabilities being sold, and malware being developed.
Leak sites and paste bins
Quickly identify stolen or leaked datasets that include your organization, your suppliers, or your staff.
Clear web sources
Get a holistic view of your online exposure with visibility into clear web sources including code repositories, social chats, CVEs, and phishing sites.
Dark web traffic
Gain visibility into Tor traffic going to and from your corporate infrastructure.
Remove Alert Fatigue
Cut through the noise of the dark web
Help your analysts triage genuine threats with the context that the dark web provides on the actions of cybercriminals. Our solutions are smart – cross-referencing new results against past findings to reduce false positives – so we’re helping you to understand your alerts, not create new ones.
Our platform doesn’t just help you find leaked company credentials in data breaches. It also helps you find credentials being discussed and shared in forums and social media chats, so you can identify (and stop) cybercriminals from actively using them.