The latest Searchlight Cyber threat intelligence report exposes how cybercriminals sell initial access to energy industry companies on dark web forums – with real examples of posts auctioning vulnerabilities in organizations around the world.
new energy industry report
Our recent survey of CISOs found that 72 percent of oil and gas companies are already gathering data from the dark web. While that is a promising start, we noted at the time that this is less adoption than in comparable high risk industries such as financial services (85 percent), manufacturing (83 percent), and transportation (81 percent). Even more concerningly, more than a quarter (27 percent) of energy industry CISOs said that they believe that activity on the dark web has no impact on their company.
The report we have released today – Dark Web Threats Against the Energy Industry – demonstrates conclusively that that is not the case by showing that energy companies are routinely discussed on dark web forums. In particular, by threat actors auctioning initial access to remote software, VPNs, and stolen credentials.
This analysis is based on a sample gathered over a 12 month period (February 2022 – February 2023) that is indicative of the types of threat actor activity that takes place on dark web sites, forums, and marketplaces.
key findings of the report
The primary takeaway of this threat intelligence is that the predominant activity we observe against the energy industry are “auctions” for initial access to corporate networks that routinely take place on popular dark web hacking forums, including Exploit and (the now defunct) RaidForums and BreachForums. The sample in this report alone includes numerous listings for organizations in countries all over the world, including targets in the USA, Canada, UK, France, Italy, and Indonesia.
These dark web auction posts have their own standard “format”. Threat actors often use the terms “Start”, “Step” and “Blitz”, which indicate the start price, the increments of the bids, and a “buyit-now” price (blitz). Most of these auction posts also list the access type along with the country of the organization, its industry, and its revenue. In some cases the name of the organization is also given.
The post in the image below is a typical example of the format and content of these posts. From the information provided by the threat actor we can determine:
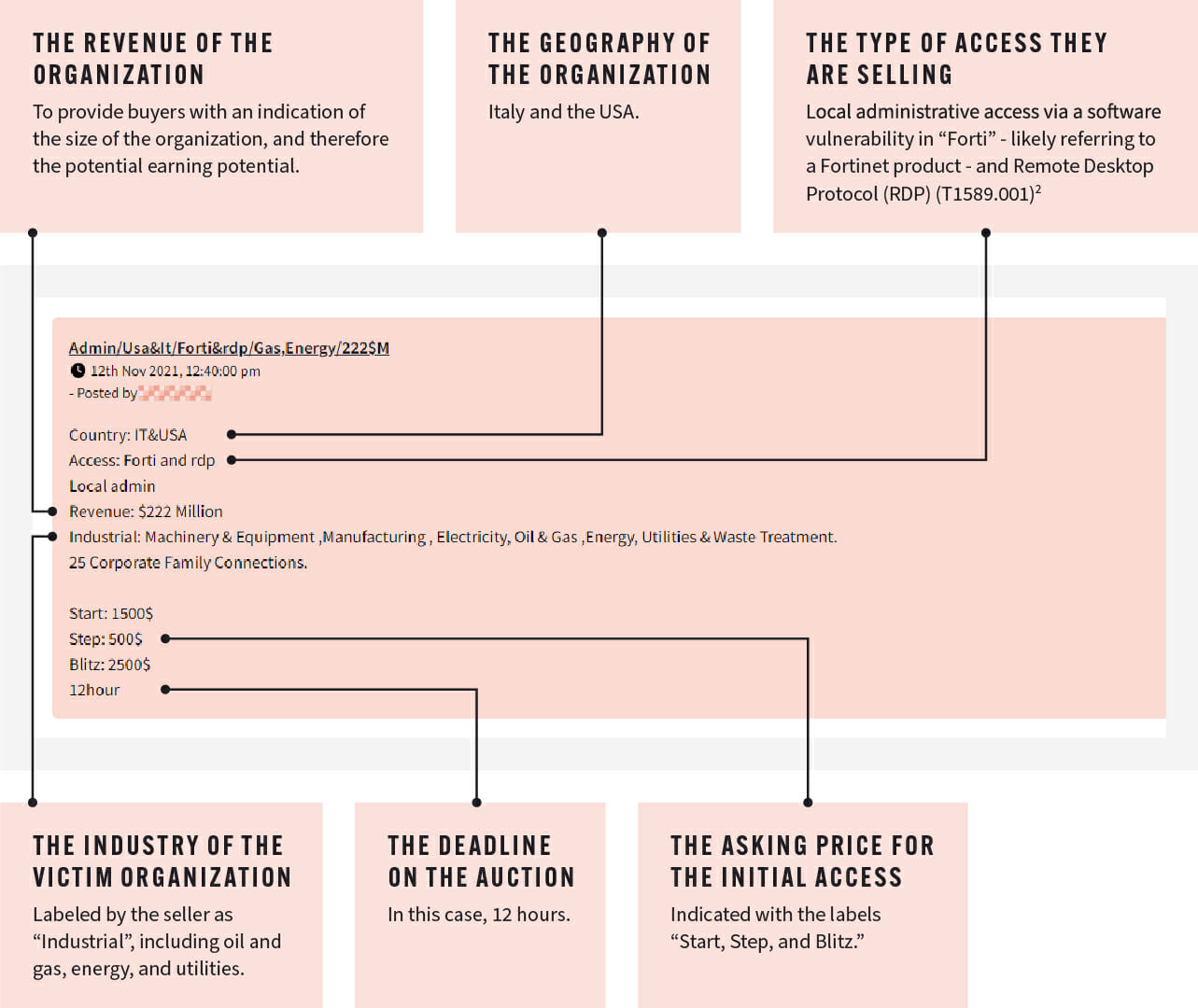
While cybercriminals share this information with the intention of attracting buyers, visibility into auction activity on dark web forums offers security professionals a valuable opportunity to identify if their organization is being targeted.
With information on the revenue, location, and technology of the potential victim, security teams can determine if they fit the profile and take mitigative action. Even if they don’t fit the exact profile of the victim, they know this is a tactic being used against other energy companies that they should factor into their threat modeling.
Threat modeling for the energy industry
While one objective of this report was to demonstrate beyond a doubt that the activity on the dark web does impact energy companies, the second – and more important objective – was to provide security teams at energy companies with advice and guidance on what they can do about it.
We have therefore combined the reconnaissance we have observed over the past year with insight into how energy companies can start threat modeling – a process for identifying, enumerating, and prioritizing threats – based on dark web threat intelligence. Where applicable, we have also provided the MITRE ATT&CK codes for the attack techniques we have observed, to demonstrate how this intelligence can practically be used by energy organizations to improve their understanding of – and defenses against – threat actors that are targeting them on the dark web.
By building threat models, and feeding them with intelligence gathered from the dark web, energy organizations can identify threats against their organizations from right at the beginning of the Cyber Kill Chain, which allows their security posture to be much more responsive to emerging attacks.