Empower your security team with the same data used by government agencies and law enforcement investigation teams to detect the earliest signs of criminals targeting your business.

Get ahead of external threats to your organization
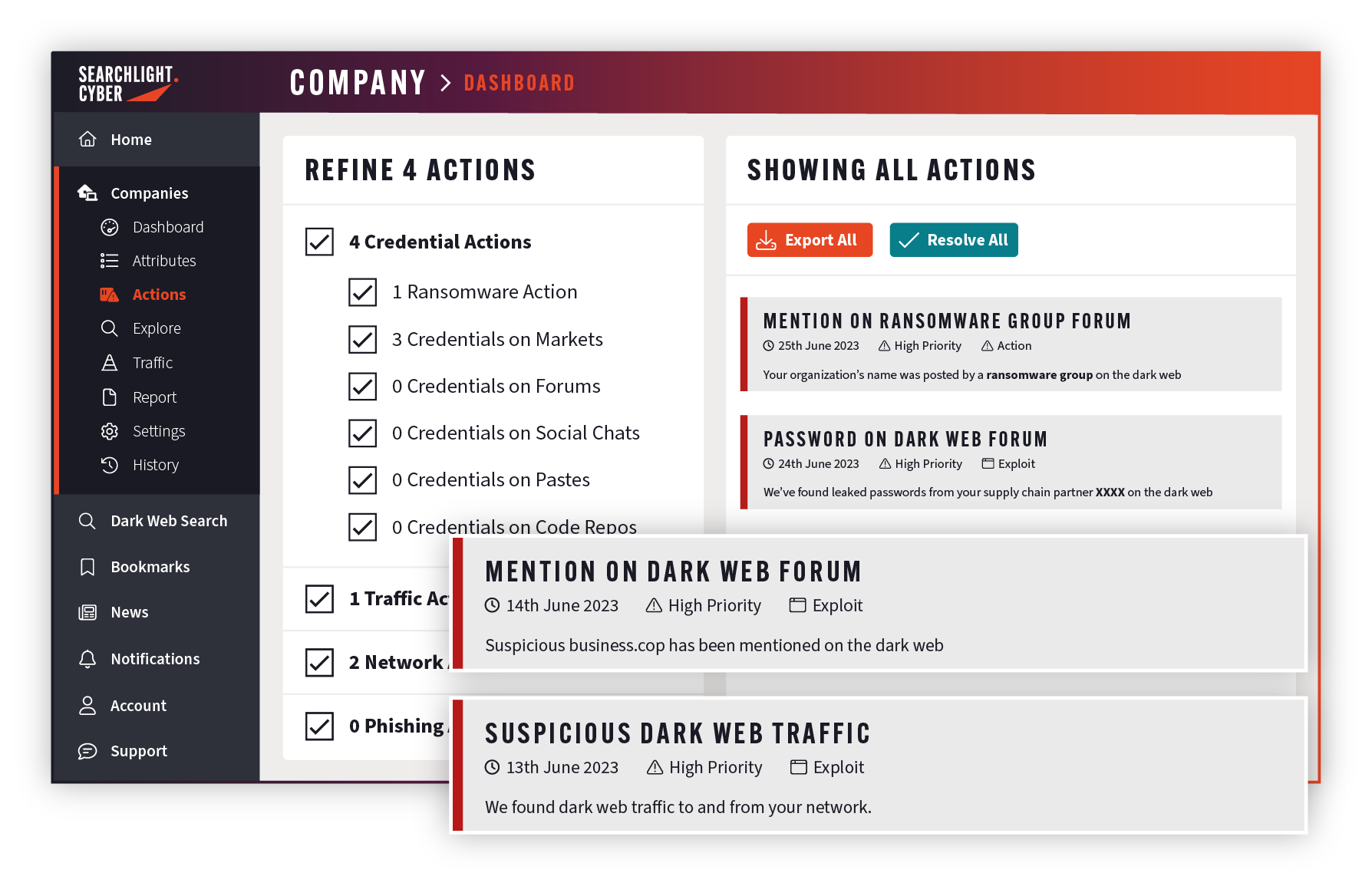
Stop manually hunting for exposures. DarkIQ is your automated analyst, continuously monitoring the clear, deep, and dark web for criminal activity targeting your organization. We detect, prioritize, and alert you to active threats against your personnel, sensitive data, and critical infrastructure – so you can zero in on what matters and remediate risks before the attack begins.
Security teams are stuck in reactive mode
Many organizations are trapped in a cycle of reactive incident response. DarkIQ empowers teams to spot adversary reconnaissance, stealer logs, and leaked data early in the MITRE ATT&CK chain – helping you shift to a preemptive security stance.
Alert fatigue hides emerging external threats
Traditional tools leave you blind to risks beyond your perimeter – unable to find real threats in the noise. DarkIQ continuously cross-references your external attack surface against over 475 billion clear, deep, and dark web records – so you can identify and act on the earliest signs of an attack.
Blind to employee and supplier data exposures
Threat actors capitalize on leaked credentials and sensitive information captured by infostealers. DarkIQ automatically identifies threats to your organization and its sensitive data, so you can take action before criminals do.
Detect exposed credentials, infostealers, and dark web chatter
Stop wasting hours triaging high-volume threat feeds. DarkIQ delivers context-rich alerts mapped to MITRE ATT&CK® techniques, empowering your team to:
- Identify compromised access: Spot breached credentials and infostealer-infected devices instantly.
- Monitor underground chatter: Track mentions of your organization across forums, marketplaces, and private Telegram/Discord chats.
- Stop attacks early: Cut through the noise and remediate exposures before your network is breached.

Disrupt phishing campaigns: Automated detection and takedowns
Work that previously took analysts weeks of manual searching is now completed in minutes.
- Rapid detection: Automatically spot malicious domains using advanced combo- and typo-squatting across 3,300+ top-level domains.
- Continuous monitoring: Track suspicious sites for active infrastructure to identify imminent attacks.
- Enhanced takedowns: Use our takedown service to remove fraudulent sites from the internet before they can be weaponized.

Detect pre-attack signals no other vendor can see
Gain visibility into Tor traffic to and from your network. DarkIQ’s advanced and proprietary network traffic analysis gives you visibility into all incoming and outgoing dark web traffic to any IP address, CIDR, or domain – enabling the preemptive detection of insider threats, data exfiltration attempts, and potential malware command-and-control activity on your network.
Learn about dark web traffic monitoringTrusted by security teams to preempt attacks
Preemptive threat detection
Make life hard for cybercriminals and protect your bottom line with DarkIQ.
Uncover hidden threatsWith DarkIQ, we were able to identify malware-infected devices belonging to our clients and takes steps to prevent account takeover attacks and protect our customers from fraudulent losses.
Spot the pre-attack signals
Mitigate threats earlier in the Cyber Kill Chain, before your network is breached.
Reduce incident response timeSearchlight has saved us a lot of time and resources – approximately 32-40 hours a month that were previously spent on research and attempting to discover new potential phishing sites.
Ready to see DarkIQ in action?
Automatically monitor for the earliest warning signs of attack to your extended attack surface.
Detect breached information, including exposed credentials, infostealers, and dark web chatter about your organization.
Gain visibility into Tor traffic to your network, helping detect insider threats, data exfiltration, and potential malware activity.