Cerberus is used globally to defend organizations, people, and countries. Let us show you how it can help you uncover and take action on dark web crime.

Criminals think you can’t see them. With Cerberus you can.
Cerberus transforms the chaos of the dark web into actionable intelligence. By providing instant access to live and historic data – including content deleted by criminals – we empower criminal investigation and threat intelligence teams to monitor illicit marketplaces, forums, and private chats, allowing them to gather evidence and take decisive preemptive action.
The dark web is a massive, unmonitored blind spot
A lack of visibility into the dark web means you are missing the early stage signals that precede an attack. With Cerberus, you can instantly investigate live sites or pivot through more than 15 years of historic dark web data to gather critical evidence.
Information overload slows down investigations
It is hard to know where to begin when starting new investigations. Our intuitive search tools, dashboards, and AI assistant help time-strapped teams surface actionable intelligence instantly – cutting manual investigation time for enterprise and government security teams.
Red tape remains an operational challenge
Navigating illicit forums and marketplaces often involves isolated "dirty machines" and red tape that slow response times. With our cloud-based virtual machine, you can go straight to the source and explore the dark web without the bureaucracy and risk to your network.

Safely search live and historic dark web data
Access over 15 years of live and archived intelligence from dark web marketplaces, forums, closed Telegram chats, and leak sites:
- Digital identifiers: Pivot from data points such as emails, crypto wallets, PGP keys, or handles to uncover full actor profiles.
- Open source intelligence: Cross-reference findings with reliable research and reporting to add critical context to your investigation.
- Vendor insights: Track dark web actors with granular data on historical goods sold, shipping preferences, payment methods, and reputation.

Cut out the manual work with the help of our AI Agent
Overcome the challenges of information overload with Cerberus’s built-in research assistant. Investigators can query our dark web data lake using simple, natural language. In response, they receive high-context, actionable intel that dramatically speeds up threat detection and evidence gathering.
- Surface relevant intelligence in minutes, not hours
- Gain instant focus on new investigations
- Reclaim your team’s time for strategic decision-making
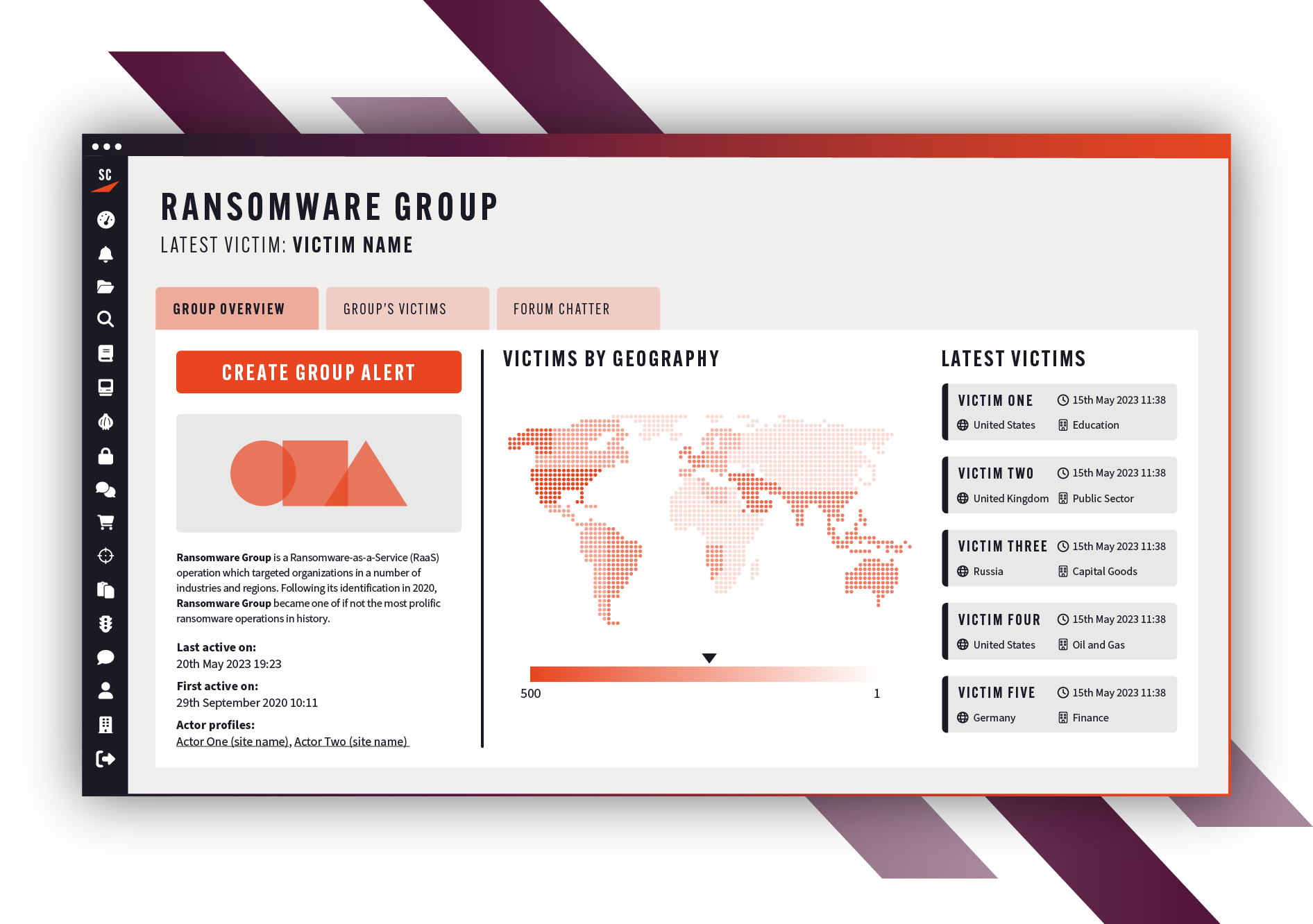
Quickly identify threats with intelligence dashboards
Cerberus gives investigations a jump start by aggregating hard-to-access data into easily searchable and filterable dashboards. Automate your monitoring, set custom alerts, and organize evidence into shareable cases from one place.
- Ransomware Search & Insights: Track active groups, victim leak sites, and breached files
- Marketplace & Forum Insights: Monitor criminal markets, vendors of interest, and hidden chats
- Initial Access Broker Dashboard: Preemptively identify listings matching your organization’s description
- CSAM Intelligence: Identify active and emerging forums and actors distributing harmful content
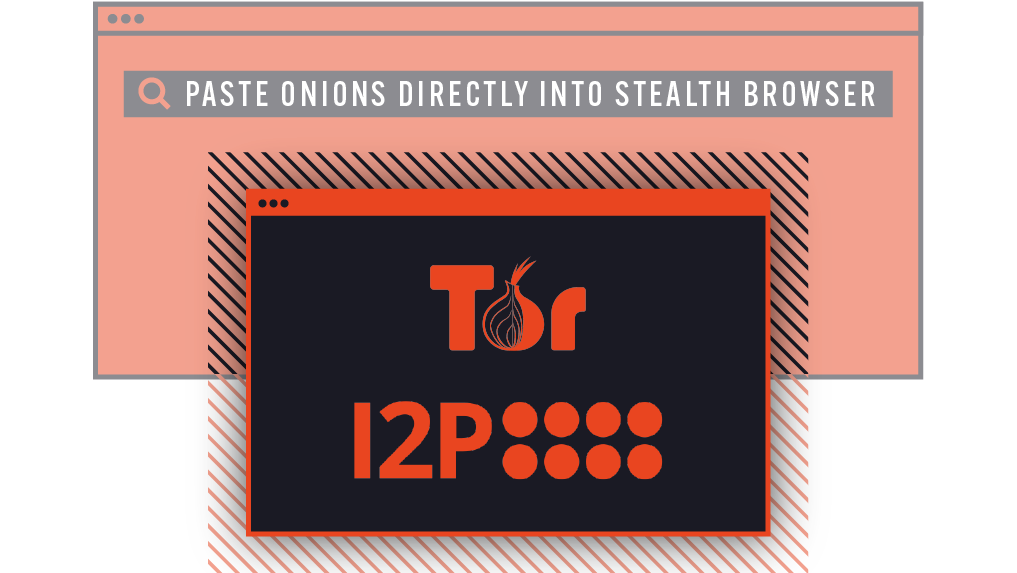
Safely investigate the dark web with our in-browser virtual machine
Cerberus’s in-platform Stealth Browser eliminates the risks of accessing the dark web by automatically masking the investigator’s digital fingerprint, allowing investigators to quickly and securely access Tor and I2P onions on the dark web without risk to themselves or their organization’s infrastructure.
Learn more about the Stealth Browser
Support critical investigations
Empower your investigative team
Stay ahead of criminals with access to Cerberus’s evidential-grade dark web intelligence.
Cerberus for law enforcementCerberus is our 'go-to tool' for all investigations. Without Cerberus, we often wouldn’t know where to begin, given how much information is on the dark web.
Support business critical investigations
Accelerate investigations, from due diligence in acquisitions to executive threat response. Cerberus’s powerful search tools help CTI teams quickly identify and report on relevant threats to their business.
Spot external threats earlierBefore we used Searchlight, conducting an investigation on the dark web was a complicated process that involved the use of an isolated computer on the network.
Ready to see Cerberus in action?
Unlock unrivaled investigative power with access to over 15 years of live and archived dark web data.
Surface intelligence faster using intuitive search, dashboards, and secure AI tools.
Go incognito to anonymously and safely investigate Tor and I2P from your browser using our stealth browser virtual machine.