In the first blog of our three part series on the messaging app Telegram, we look at why the app is so popular with criminals and some of the illicit goods and services on sale on Telegram channels – from phishing sites to Refund-as-a-Service operations.
what is telegram?
Telegram is an instant messaging and communication application available on computers running various operating systems and mobile devices. As of January 2023, the application has more than 700 million monthly active users, accounting for approximately 8.7 percent of the global population. While this puts it behind comparable apps, such as Whatsapp, WeChat, and Facebook Messenger, it’s still an extremely large user base and Telegram is noteworthy for attracting users that value privacy including – as this blog outlines – a criminal element.
There are a number of reasons why Telegram has become so popular. Firstly, it’s free to use. While Telegram did launch a Premium version in June 2022 with additional features, reports suggest that the vast majority of users continue to use the free version. It also has functionality for different types of communication. For example, users can communicate in private conversations, group chats, or participate in one-way channels where only the administrator can post, with this last feature often used for “news” delivery. Voice and video communication is also offered but, according to our observations, these features are rarely used by the criminal ecosystem on Telegram.
However, one of Telegram’s biggest draws is its perceived privacy in comparison to other apps. Registering for an account only requires a valid phone number and once an account is created users have the option of hiding it and just displaying a username. Telegram also has privacy features such as automated self-destruct messages and “Secret Chats” that are end-to-end encrypted. Many users are also attracted by Telegram’s relatively independent ownership compared to similar apps run by large corporations, which relieves concerns about data being harvested, sold, analyzed, or otherwise exploited.
How is telegram used by cybercriminals?
The privacy features, anonymity, and low barrier of entry to Telegram has attracted criminal users for years. Telegram has a diverse and flourishing cybercriminal user base, which includes (but is not limited to) cybercriminals selling network access and stolen data, ransomware groups, politically motivated hacktivists, distributed denial of service (DDoS) operations, and more. These cybercriminals often also have a presence on deep and dark web hacking forums and marketplaces but use Telegram as a channel to communicate among themselves or to reach a broader audience.
This blog series focuses predominantly on how cybercriminals use Telegram to target both companies and individuals through fraud schemes. According to our observations, financial fraud is extremely prevalent on Telegram, with numerous group chats and channels being used by criminals to discuss their operations, share techniques, and find buyers.
refuNding-as-a-service on telegram
One such example is refunding fraud, a scheme that abuses a retailer’s return policy. Criminals purchase various goods and return the products to the seller in order to get the money refunded. However, the returned products are replaced with counterfeits, stolen items, stripped of their valuable parts, or are completely different to the product originally purchased. Alternatively, fraudsters claim that they received empty boxes or products unrelated to the intended purchase in order to receive a refund.
This type of fraud is commoditized on dedicated Telegram channels that offer “Refunding-as-a-Service”. Individuals purchase a product and share their order information with the Refund-as-a-Service operator, who makes the request to the retailer on their behalf and uses social engineering techniques to ensure the request is approved. When the refund is granted the Refund-as-a-Service operator takes a percentage of the money or receives a set fee.
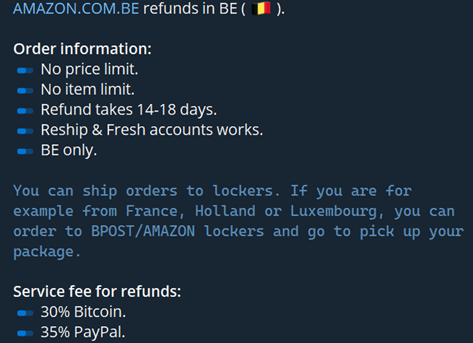
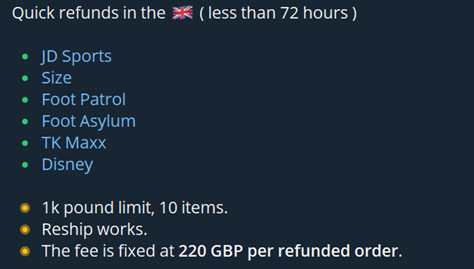
For example, in the screenshots below one Refund-as-a-Service operator targeting Amazon has a 30% service fee if the buyer pays in Bitcoin or 35% fee for paypal, while another operator charges a flat fee of 220 GBP per refunded order and stipulates that the buyer must order goods of more than one thousand pounds.
When needed, scammers also employ more advanced techniques, such as simulating the product return process without actually sending the product back. For this process, boxing services are used, allowing the scammer to modify the parcel’s return label. Sometimes disappearing ink is used in order for the package to become lost in transit.
Sale of illegal commodities
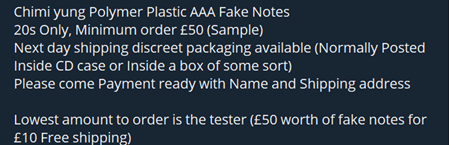
Telegram channels are also being used widely by actors to sell a number of illicit items, including drugs, weapons, jewelry, stolen goods and much more. Most often, commodities are closely related to financial fraud. Examples include the sale of fake bank notes:
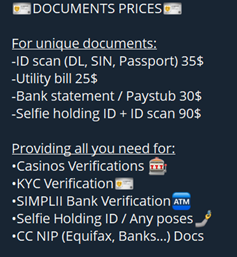
Forged or stolen identity documents:
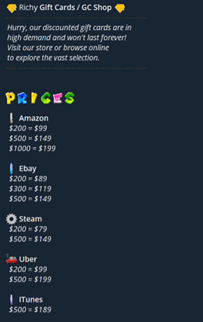
And gift cards:
While it is quite obvious why anyone would buy fake bank notes at a hugely discounted price, it might not be so clear why stolen or fraudulent identity documents are in such high demand. However, there are a number of uses for cybercriminals: documents can be used to open bank accounts, apply for loans or government aid and tax returns, bypass cryptocurrency exchange verifications, travel in and out of the country, to name just a few reasons. Meanwhile, gift cards are widely available on Telegram marketplaces as fraudsters usually purchase them with stolen credit cards and resell them for up to 50 percent of their value in cryptocurrency.
phishing pages
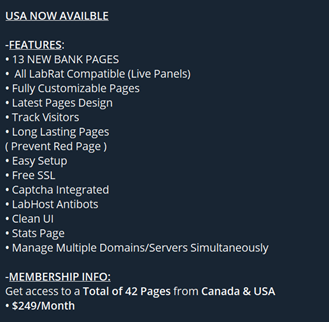
Cybercriminals also use Telegram channels as a marketing tool to advertise and sell phishing pages – fake websites that mimic legitimate brands to steal the personal information of unsuspecting users, such as bank account details, full name, address, date of birth, and social security number. The most targeted industries include banking and financial institutions, telecommunications companies, and governmental entities.
We have observed some vendors developing simple, static pages that are sold for as little as 50 USD, while others claim to be able to develop fully customizable pages with live administration panels that would allow the attacker to control the victim’s journey on the page step-by-step.
These more complex phishing sites are valuable because they allow cybercriminals to request specific information they need to commit fraud against the victim’s account in real time. For example, if the cybercriminal is being blocked by a multi-factor authentication (MFA) request, they could request the one-time-password from the victim on the fake site. Some services also offer anti-bot protection systems as well as a CAPTCHA module:
The buyer of the phishing sites can either use the data they gather themselves to commit fraud against the victim or package up the data and sell it on for other cybercriminals to use. Of course, this activity takes place on Telegram as well…