In the second blog in our series on dark web developments in 2023 we take a look at the profiles of some of the most active threat actors of the year and assess the motivations that drove cybercriminal activity over the past 12 months.
threat actors in 2023
A lot can happen in a year in cybersecurity, and 2023 was no exception. This series of blogs is a retrospective of some of the top trends, changes and continuities observed by Searchlight Cyber’s Threat Intelligence team, covering areas such as cybercriminal forums and marketplaces, threat actor motivations, malware, ransomware, initial access brokers, vulnerabilities, and social engineering techniques. The platforms, tools, actors and insights featured in this series are based on intelligence gathered from Searchlight’s extensive deep and dark web dataset.
You can find the previous blog in the series here: Hacking Forums and Dark Web Marketplaces.
In this entry, we examine the motivations behind cybercriminal activity in 2023, a year where geopolitical developments spurred on state-sponsored attacks and hacktivist activity. Nevertheless, financially motivated crime retained its prominence on the dark web, and we take a particularly forensic look at some of the most prolific Initial Access Brokers of the year, and how they made their cash.
financially motivated threat actors
The vast majority of the blackhat scene consists of financially motivated actors – such as Initial Access Brokers (IABs), ransomware operators, database sellers, malware developers and many, many others. These actors have one main purpose that fuels their work: money. These actors appear and disappear from dark web forums and sites depending on their objectives – some choose to remain active as long as there is money to be made, while others choose to set a goal and, once that goal is reached, they vanish.
initial access brokers (iabs)
IABs are some of the most prolific financially-motivated threat actors that we observe on the dark web. These cybercriminals specialize in obtaining access to victim’s networks and selling that foothold onto other threat actors to exploit – typically advertising their access on dark web forums for others to bid on.
IABs use a range of techniques to achieve this access: some operate malware, some use social engineering, more technical actors exploit vulnerabilities, while others recruit malicious insiders. The method isn’t particularly relevant to customers of IABs (which could include ransomware operators, database vendors, and members of cyber-espionage groups), they just want the job done. This large and diverse customer base goes some way to explaining why there is such a thriving market of IABs, it’s a lucrative and relatively low-risk portion of the Cyber Kill Chain to own. According to our observations, some of the most prolific IABs of 2023 include:
el84
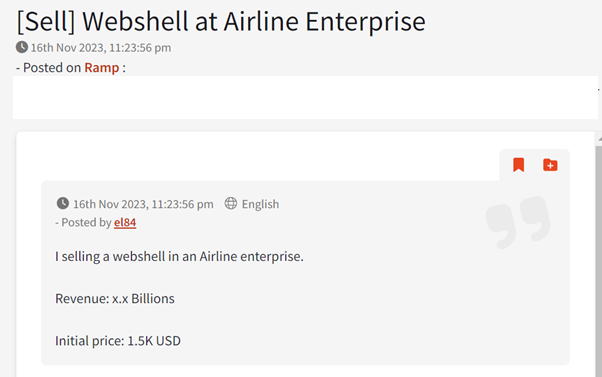
The threat actor using the el84 moniker (as well as other alternative handles that we have linked to the same persona) became active on XSS, Exploit, and Ramp cybercrime forums in January 2023. Since then, they have made more than 120 posts on each forum and have obtained a significant reputation in the cybercriminal underground, along with positive feedback from buyers. It quickly became clear that el84 is a knowledgeable, financially-motivated IAB who also provides technical advice and guidance to other actors.
Examples of key TTPs observed include:
- Selling unauthorized web shell access.
- Selling information about vulnerabilities allowing remote code execution (RCE).
- Selling compromised VPN credentials.
- Offering to deploy customers’ (aka other cybercriminals) malware on compromised networks.
Examples of targeted industries:
- Governmental entities.
- Law enforcement.
- Aviation.
- Telecommunications.
- Automotive.
- Education.
- Technology.
- Banks.
An example of an advert for initial access being sold by el84 on the Ramp hacking forum.
Bl4ckB1rD/RobinHood
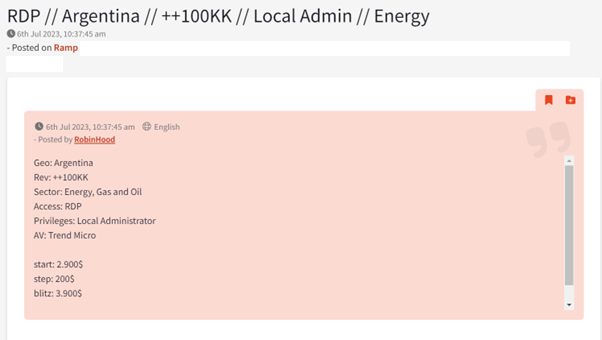
The threat actor using the Bl4ckB1rD, RobinHood, and other alternative handles is another specialist in the sale of initial access. They are a member of the XSS and Ramp forums, but were recently banned from Exploit after a dispute with another threat actor. Bl4ckB1rD/RobinHood has recently enhanced their capabilities and started selling exfiltrated databases. Furthermore, the threat actor developed a ransomware strain using the Go programming language, which they have dubbed Kuiper and started offering under the Ransomware-as-a-Service model.
Examples of key TTPs observed include:
- Selling unauthorized web shell access.
- Selling compromised RDP and VPN credentials.
- Offering to work on percentage of profits.
- Dumping and selling compromised data.
- Operating ransomware.
Examples of targeted industries:
- Governmental entities.
- Finance.
- Public sector.
- Insurance.
- Utilities.
- Transport.
- Manufacturing.
Example of an initial access advert posted by the threat actor RobinHood on the Ramp hacking forum.
maveboy
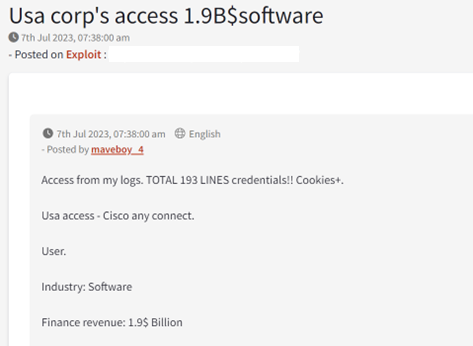
The threat actor using the maveboy handle is a member of the Exploit cybercrime forum who became active in February 2023. Based on our observations, the actor has completed several sales of access to entities around the world and quickly obtained a positive reputation score of 11 points on the forum. maveboy appears to source their access credentials from stealer logs while also showing evidence of leveraging software capable of brute-forcing accounts. The actor’s choice of targets appears to be opportunistic, with revenues ranging from US $5million and up to just under US $2 billion.
Examples of key TTPs observed include:
- Selling initial access.
- Selling VPN and RDP accounts.
- Discussion about brute-forcing tools.
- Showing interest in network checkers, malware droppers.
Examples of targeted industries:
- Insurance
- Finance.
- Supply chain.
- Pharmaceuticals.
- Energy.
- Transportation.
Example of an initial access advert posted by the actor maveboy on the Exploit Forum
for more information on iabs read our mitigation guide: COMBATTING INITIAL ACCESS BROKERS WITH DARK WEB INTELLIGENCE
state-sponsored threat actors
State-backed threat actors are funded and coordinated by government entities from specific countries such as (but not limited to) Russia, China, Iran, and North Korea. They engage in a range of activities including cyber-espionage, sabotage, use of destructive malware against high-impact targets and critical infrastructure, as well as coordinating propaganda and disinformation campaigns. In some cases, state-sponsored actors have been observed to act as financially motivated actors as well, for example – stealing millions in cryptocurrency. Having the support of their government usually means that the hacking groups do not have to worry about law enforcement and can focus their (often vast) resources on cybercrime.
These advanced persistent threat (APT) groups are known to have long dwell times on compromised networks, allowing them to carefully analyze and propagate their payload, maximizing the impact on their victim. One example of a state-sponsored APT group increasing their activity in 2023 was Gamaredon, a group considered to be backed by the Russian government. In a report released by the National Security and Defense Council of Ukraine, the group was credited with significant capabilities, leveraging a combination of malware laced legitimate tools, spear-phishing, and remote access trojans to conduct data theft and espionage campaigns in the context of the invasion of Ukraine by Russia.
hacktivism
Hacktivists choose their victims based on factors such as geopolitics, religion, social issues, race, or other values. Unsurprisingly, the ongoing war in Ukraine has also continued to fuel global hacktivism in 2023. For example, in December 2023 a hacktivist group known as Solntsepek, which has suspected ties to Russian military intelligence, claimed responsibility for the cyberattack against Ukraine’s biggest mobile operator on its Telegram channel. Of course, this activity takes place on both sides – on the same day Ukrainian intelligence claimed its own attack on the Russian Federal Tax Service, using wiper capabilities to destroy databases and backups.
The outbreak of the Israel-Hamas conflict also resulted in a noted increase in hacktivism. Pro-Hamas groups such as the Islamic Hacker Army, Cyber Toufan, Cyber Av3ngers, Electronic Tigers Unit, AnonGhost and VulzSec targeted Israel with attacks – for example, conducting data wiping attacks, sending fake nuclear threat notifications, and even targeting Israeli-made critical infrastructure used in the US. Pro-Israel hacktivist groups like Unknown CyberCult, Garuna Ops, BlackDragonSec, and Indian Cyber Force have also joined the conflict, for example targeting Palestinian government services and the Hamas official website.